Majority of business execs in SEA anticipate data theft, APT, and ransomware attacks
With the many news reports highlighting the damages of cyberattacks against businesses and countries as a whole, Kaspersky’s fresh study revealed the heightened awareness of business executives in Southeast Asia (SEA) about the sophisticated risks online. Data theft, alongside Advanced Persistent Threat (APT) attacks and ransomware infections, are the highest on their list of concerns.
The study titled “How business executives perceive ransomware threat” surveyed a total of 900 senior non-IT management (such as CEOs, VP, and Director level) and business owners or partners at companies with 50—1000 employees. Conducted last April, the study was done globally with 100 executives from SEA.
 |
| Kaspersky’s study however uncovers that more than half believe a ransomware attack against their business “is too small to worry about” |
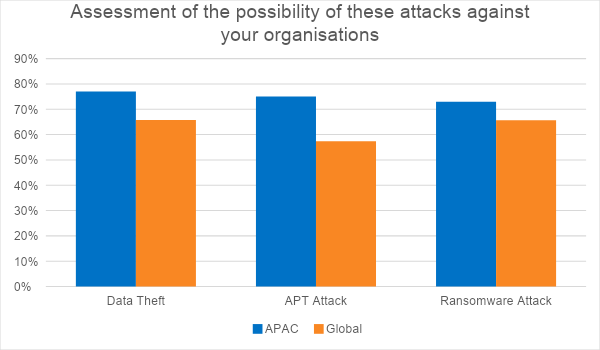
When asked to assess the possibility of different types of cybersecurity incidents, data theft, also known as data breach, is the threat that the respondents from SEA are most concerned about (77%). This does not come as a surprise as news about data breaches across the region were being reported almost regularly with wide victimology from e-commerce companies, digital services provider, hotel chains, insurance and health companies, and even government agencies.
Data theft – the illegal transfer or storage of personal, confidential, or financial information – is closely followed by an APT attack (75%), and a ransomware attack (73%).
An APT attack uses continuous, clandestine, and sophisticated hacking techniques to gain access to a system and remain inside for a prolonged period of time, with potentially destructive consequences. Because of the level of effort needed to carry out such an attack, APTs are usually leveled at high-value targets, such as nation states and large corporations, with the ultimate goal of stealing information over a long period of time.
Ransomware, as the name suggests, is malicious software designed to block access to a computer system or encrypt its data until a sum of money (a ransom) is paid. These attacks have been carried out on individuals or corporations.
The anticipation for these three damaging attacks is higher among SEA-based business leaders as compared to the global average by more or less double-digit margins.
However, the same study revealed that while the majority of the respondents anticipate a ransomware attack, almost 7 in every 10 (65%) of them believe that “the possibility of my organization being exposed to a ransomware attack is too small to worry about”.
A majority (81%) of the surveyed non-IT executives in SEA also trust that the security measures they have in place are enough to protect them from a ransomware attempt.
“At first glance, it is good to see that the business executives here are confident about their security posture to defend their organizations against damaging online attacks such as ransomware. We should, however, be careful about not letting confidence breed complacency because the reality is a ransomware attack is not something too small for enterprises to be worried about,” comments Yeo Siang Tiong, General Manager for Southeast Asia at Kaspersky.
“Even though 72% of our respondents from SEA believe that ransomware attacks are being shown as a bigger threat than they actually are by the media, this type of threat is actually evolving and is transforming into a bigger menace that our security systems and IT staffs should be ready for,” adds Yeo.
Since 2020, Kaspersky experts have been warning about “Ransomware 2.0”. Almost always a “targeted ransomware”, Ransomware 2.0 refers to cybercriminal groups who moved from hostaging data to exfiltrating data coupled with blackmailing. The aftermaths of a successful attack include significant monetary loss and damaging reputation loss.
This type of attack goes beyond kidnapping a company’s or an organization’s data. These groups are utilizing the increasingly valued digital reputation to force their prey to pay a hefty ransom.
As of 2020, at least 61 entities from the region were breached by targeted ransomware groups including companies from light industry – including the manufacturing of clothes, shoes, furniture, consumer electronics and home appliances; public service, media and Technology, heavy industry – including oil, mining, shipbuilding, steel, chemicals, machinery manufacturing; finance, and logistics.
The infamous ransomware groups Kaspersky experts closely monitor include REvil, LockBit, Conti, and more.
To help organizations protect their systems from ransomware and other sophisticated attacks, Kaspersky experts recommend the following:
- Always keep up-to-date copies of your files so you can replace them in case they are lost (e.g. due to malware or a broken device). These should be stored not only on a physical device but also in cloud storage for greater reliability. Make sure you can quickly access your backups in the event of an emergency.
- Keep your OS and software patched and up to date.
- Train all employees on cybersecurity best practices while they work remotely.
- Only use secure technologies for remote connection.
- Carry out a security assessment on your network.
- Enterprise companies are recommended to use anti-APT and EDR solutions, enabling capabilities for advanced threat discovery and detection, investigation and timely remediation of incidents, as well as to have access to the latest threat intelligence. An MDR provider could help to effectively hunt any advanced ransomware attack. All of the above is available within Kaspersky Expert Security.
- Follow the latest trends via premium threat intelligence subscriptions, like Kaspersky APT Intelligence Service.
- Know your enemy: identify new undetected malware on premises with Kaspersky Threat Attribution Engine.
- If you become a victim, never pay the ransom. It won’t guarantee you get your data back but will encourage criminals to continue their business. Instead, report the incident to your local law enforcement agency. Try to find a decryptor on the internet – you can find some of these available at nomoreransom.org.
- Never follow the demands of the criminals. Do not fight alone - contact Law Enforcement, CERT, security vendors like Kaspersky.
For companies looking to improve the expertise of their in-house digital forensics and incident response teams, as well as for IT security practitioners looking to upgrade relevant skills, Kaspersky has also expanded its online expert training portfolio.
The Windows Incident Response training was developed by experts from the company’s Global Emergency Response Team (GERT) with more than 12 years’ experience in the field.
The self-guided training course includes 40 video lessons and 100 hours of virtual lab time for hands-on learning. The estimated training duration is 15 hours, but participants will have six months of access to the platform to finish the training.
More information about the Windows Incident Response course is available via this link.












No comments: